Qakbot, a notorious malware, has made a comeback just months after being shut down by the FBI and other law enforcement agencies. Despite the takedown efforts, the Windows botnet has reemerged, posing a renewed threat to cybersecurity.
The Resurgence of Qakbot
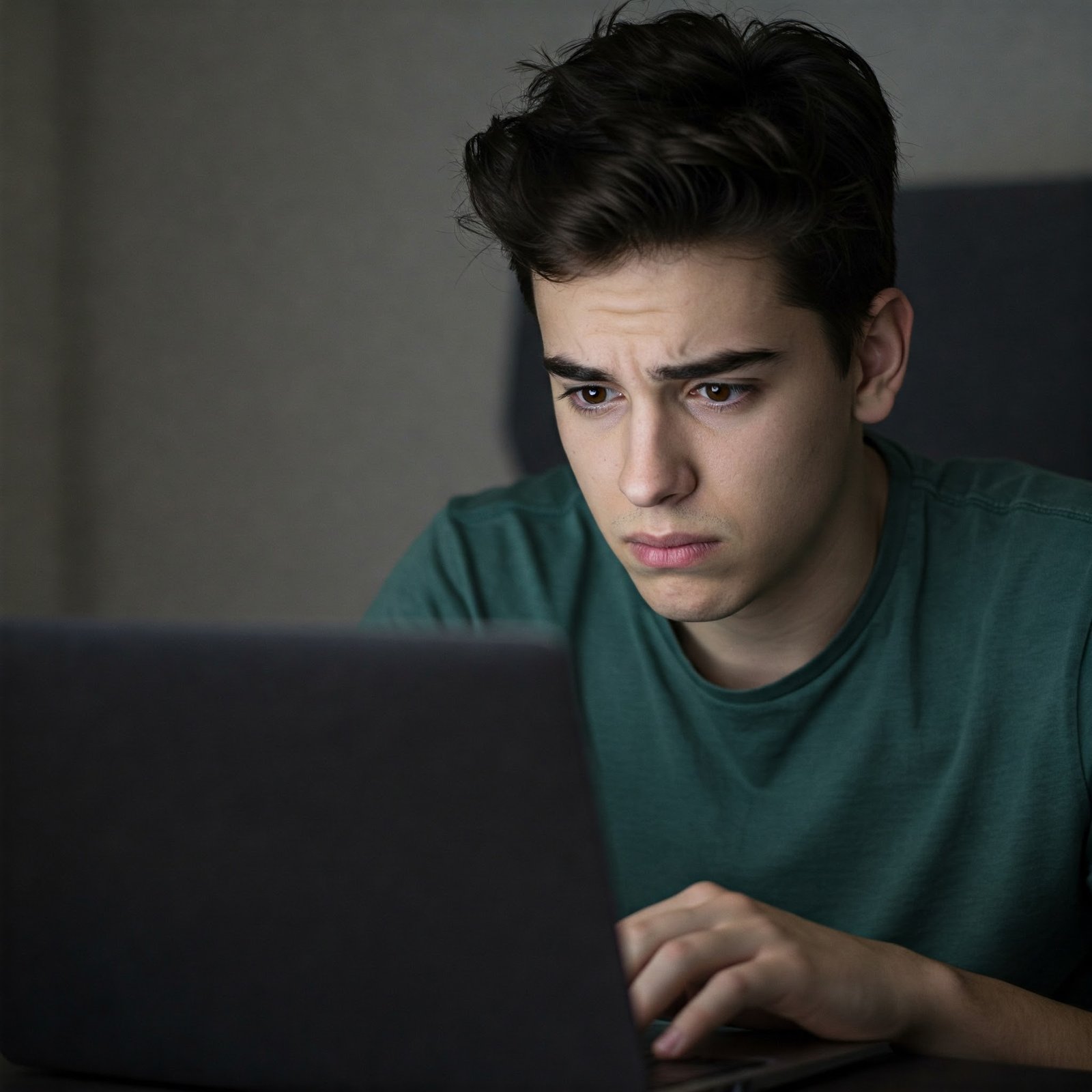
Multiple sources have confirmed the return of Qakbot malware. According to Microsoft Threat Intelligence, a new Qakbot phishing campaign has been active since December 11. However, the attack attempts are currently low in volume. The gang behind Qakbot targets the hospitality sector, employing phishing emails with craftily doctored PDF attachments that appear to originate from the US Internal Revenue Service (IRS) to deceive their victims.
Attack Methodology
The Qakbot phishing campaign employs a clever tactic. When the malicious PDF attachment is opened, the target is presented with an error screen indicating that a preview of the document is unavailable. However, a seemingly innocuous button is provided, prompting the user to download the document from “AdobeCloud.” Clicking this button initiates the download and installation of Qakbot, potentially an updated payload. Microsoft’s analysis reveals that the latest version, 0x500, was generated on December 11. Researchers at Proofpoint have also confirmed Qakbot’s resurgence, noting minor tweaks in its new features. Interestingly, Qakbot’s activity can be traced back to November 28, preceding Microsoft’s initial identification.
Previous Takedown Efforts
Qakbot’s revival echoes the challenges faced in combating cybercrime. Operation Duck Hunt, led by the FBI, resulted in the takedown of Qakbot in August. This operation involved the seizure of Qakbot’s infrastructure and the crypto wallets of 20 of its operators. Despite the involvement of authorities from the UK, France, Germany, the Netherlands, and Latvia, no arrests were made. The FBI hailed Operation Duck Hunt as a significant operation against a botnet, showcasing the technological and financial prowess of the Department of Justice. However, the return of Qakbot shows how hard it is to get rid of cyber threats without catching the people responsible.
Understanding Qakbot Malware
Initially emerging as a banking trojan in 2008, Qakbot, also known as Qbot or Pinkslipbot, has evolved into a multifaceted malware delivery service. Its primary objective shifted from stealing banking credentials and committing financial fraud to partnering with threat actors for ransomware attacks, espionage, and data theft. Qakbot spreads through phishing campaigns using various lures, such as reply-chain email attacks. These campaigns employ stolen email threads to trick recipients into opening malicious attachments or downloading infected files. The malicious documents used in these campaigns range from Word or Excel files with malicious macros to OneNote files with embedded files, ISO attachments, and Windows shortcuts. Qakbot leverages these documents to exploit vulnerabilities in Windows, infecting victims’ devices upon execution. Once installed, Qakbot injects a DLL into legitimate Windows processes, enabling it to persistently operate in the background and deploy additional payloads.
Key Capabilities of Qakbot
Qakbot possesses several key capabilities that make it a significant cybersecurity threat:
1. Information theft
Qakbot specializes in stealing sensitive financial information, including login credentials, banking details, and personal data.
2. Network propagation
Qakbot has the ability to spread laterally within a network, infecting multiple machines and compromising network security.
3. Payload delivery
Qakbot serves as a delivery mechanism for other malware, including ransomware, allowing threat actors to launch devastating attacks.
4. Keylogging
Qakbot records keystrokes, capturing login credentials that can be exploited for further malicious activities.
5. Email credential theft
Qakbot harvests email credentials, facilitating additional attacks such as spam campaigns, amplifying its impact.
Parallels with Emotet’s Resurgence
Qakbot’s return is reminiscent of Emotet, another notorious malware that resurfaced after being taken down by international law enforcement agencies in 2021. Like Emotet, Qakbot’s persistence underscores the challenges in permanently neutralizing such threats. At its peak, Emotet controlled over 1 million machines, solidifying its position as one of the most advanced botnets globally.
Final Thoughts
The resurgence of Qakbot malware following a brief hiatus highlights the ongoing challenges in combating cyber threats. Despite the efforts of authorities and international cooperation, cybercriminals continue to adapt and revive their malicious activities. It is important for users to stay vigilant and take precautions to protect themselves against such threats.
Related reading:
- What is Qakbot? – Darktrace
- Qakbot’s backbot: FBI-led takedown keeps crims at bay for just 3 months – The Register
- Qbot malware returns in campaign targeting hospitality industry – BleepingComputer
- Qakbot Malware – BlackBerry